The smartphone industry is dominated by Android devices, but one thing you’ll have to deal with is that the Google-owned OS is one of the most vulnerable platforms there is, especially when compared to close rival Apple’s iOS.
Nevertheless, I have to admit that switching from Android to a different OS is not just in my DNA – at least not in the foreseeable future. Despite this strange liking for the OS, most people will agree that Android is wrecked. Interestingly, it’s the best feature of the OS that makes it the most vulnerable – the open source nature.
Here’s a short explanation:
Android OS is owned by Google and as you may know, this OS is just a combination of complex source code files and it isn’t a standalone product. What not being “standalone” means here is that in order for the OS to be complete, someone has to pick up these files and actually build a working product from the same, which is then distributed inside phones.
Whether it’s you or me – Android OS is open to anyone. You can pick up these source code files, tweak them and build your own personalized version of the OS, which you can then distribute inside a personally branded device, be it a phone or tablet. This is possible because a huge chunk of this Android OS’ code is open-ended, allowing anyone with some knowledge of how programming works to change the files in a unique way suitable to themselves. This is how we end up with unique experiences on Samsung, LG, Motorola, Sony, Oppo, OnePlus, Xiaomi, LeEco, Infinix, Tecno devices and so on, yet the underlying OS is the same Android.
The fact that Android OS is open-ended has also allowed Google to encourage third-party experts to scan the code and attempt to break it or in simpler terms, they assume the role of hackers. In this way, they are able to discover any security vulnerabilities, bugs, and exploits in the OS and alert Google about them. In fact, the search engine giant usually rewards these discoveries with huge cash incentives, something that encourages more security experts to dig deeper.
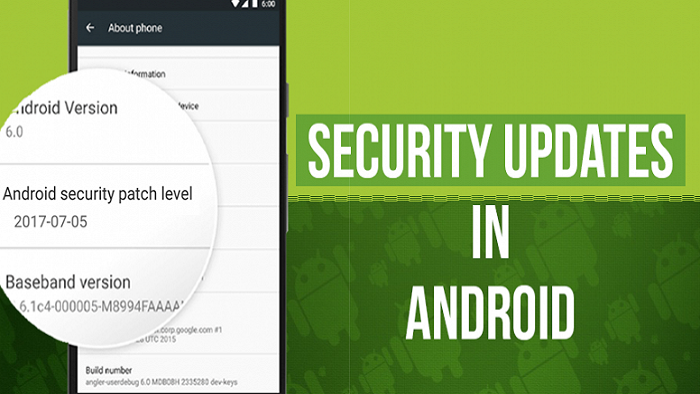
In August 2015, Google introduced monthly security updates. Essentially, Google collects information from third parties regarding the bugs, exploits and other security vulnerabilities they’ve found in the OS on a monthly basis. When they receive this info, the experts at Google try to edit the OS’ source code files in order to seal the security holes discovered in the OS over the same period. Well, for one thing, it’s not an easy ride in the park when code maintenance comes into play; however, you can’t separate it from responsible software development.
Since Google cares for its users, it pays people to actually maintain the Android OS code. These are the people who edit the code with fixes to issues discovered by the in-house team as well as third parties looking to win themselves some good cash. When done with editing, the updated changes are then published by the company, including a bulletin that details out everything that the update actually brings. Once this bulletin is published, Google Pixel and Nexus devices get a small update over the air – which is the monthly Android security patch we are actually talking about.
As you can see, these updates – which come out monthly – have fixes for security holes, exploits, and bugs that might affect – or already affecting – all Android devices and not just the Google Pixel and Nexus products. This is why the company also makes the edited or rather updated source code files available to all of its Android partners – the partners that make the phones that we use, be it Samsung, LG, Motorola, Xiaomi, Oppo, BlackBerry, Nokia, Infinix, Tecno, OnePlus, or whatever brand.
Some of these brands have been showing really impressive commitment towards rolling out these updates to their devices, no matter how late. But lately, the likes of Nokia, BlackBerry, OnePlus, and even Samsung have really stepped up, rolling out these updates to their top-tier devices a week or so after the Google Pixel and Nexus products receive the same treat. However, some devices have never received these monthly Android security updates.
Just so you know, monthly Android security updates are the most important you can have on your phone. Of course, no one hates the idea of updates that carry new features or even a whole new OS, however, you need to understand that these monthly security updates are what actually make your phone capable of serving you better. If you don’t believe this, take some time and read this month’s Android security patch bulletin and see all that it brings. You’ll be scared!

With the number of hackers out there growing day by day, someone will at some point do something crazy, especially since they know that there are lots of Android devices out there that are not patched. To make it worse, their manufacturers have no plans of sending out fixes for the many security vulnerabilities they’ve possibly developed over the months or years they’ve been in use. One day you’ll wake up to an alert that asks you to send $300 or more to some weird account so as to access your beloved Android phone’s contents. And this will be the real Android security Armageddon.
Is there a possible solution?
So, now that we’ve seen how wrecked Android OS is, the question many will be asking is whether there’s a way around this. Well, for sure, it’s almost impossible. As noted earlier, the power or rather beauty of Android is underlined by the open-ended nature of its source code. When Android partners get their hands on the Android source code files, they play around with them so much that it makes it impossible to simply come in with the updated (monthly) source code from Google, drop it in there and still have things as they were. It actually requires another sit-down.
To take care of this, the only solution would be these Google partners to stop messing too much with the core of the OS, but as noted, it’s where the beauty of Android lies, which cannot just be skipped. These companies want to have their own versions of Android in order to incorporate their own software and services and as such, they’ll have to handle most of the fixing on their own. This is actually why Samsung and other serious OEMs also detail monthly Android security updates’ bulletins, just after Google does the same. They do so because they know their phones run in-house software on top of the stock Android OS and as such, they similarly have their in-house security issues to handle.
As you may know, smartphone OEMs sell phones on their own or through third-party retailers such as wireless carriers. Usually, these carriers request for special devices with the Android software further customized to their needs. So, for instance, Safaricom users may get a Phantom 6S that has Tecno’s own software in addition to the carrier’s own software and customizations. This makes the already long chain of people calling the shots even longer.
Now, this prolonged chain gets even worse when some smartphone OEMs think that some of the phones they developed themselves aren’t worth their time, money and resources needed to maintain the code, which sums up the major reasons many Android smartphone owners out here never receive their deserved monthly Android security patches.
It’s just the way Android works, but Google has been working on a way to fix this through Project Treble. This feature, which will be preinstalled on all Android devices running Oreo and above, will shorten the whole process of rolling out software updates. Still, the best people that can fix this wreck, however, are smartphone makers. They need to man up and start making our phones safe by ensuring that monthly Android security updates are available to all of their devices. After all, we paid for them, no matter how little. This is a very important aspect to look at when buying your next Android phone.
Meanwhile, do you regularly receive Android security updates on your device? Let us know in your comments below.